Picture this: Your Transportation Management System (TMS) shows your high‑value freight moving calmly toward its destination. Everything looks fine. In reality, the truck was rerouted to a hidden warehouse hours ago. By the time you notice the anomaly, the cargo is gone—an example of how modern cargo theft unfolds.
Welcome to the new era of cargo theft. In 2026, the North American logistics industry is facing an unprecedented fraud crisis. Cargo theft is no longer about physical breaches alone. Today, we are up against highly organized criminal networks armed with sophisticated tactics and AI-driven attacks.
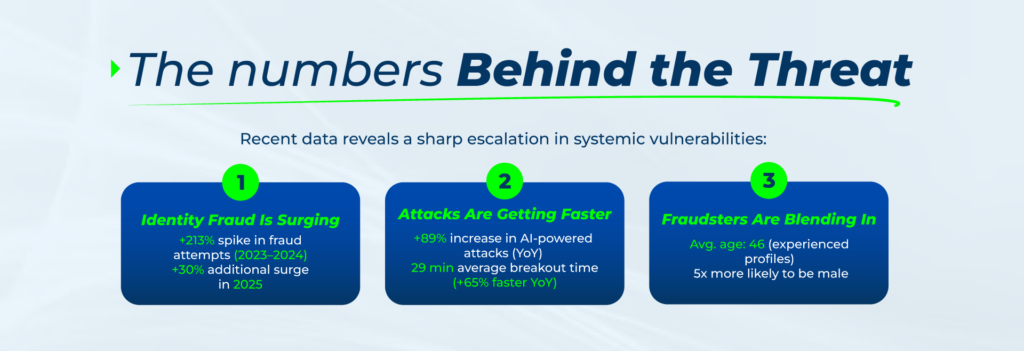
This isn’t just local organized crime. Advanced state-nexus cyber activity—specifically operations linked to China—grew by 38% across all global industries in 2025. However, the logistics sector took the absolute heaviest hit, suffering a staggering 85% surge in targeted attacks.
For logistics leaders, protecting operations from financial and reputational loss in this landscape is non-negotiable. That’s why we are breaking down how these new threats operate and, most importantly, the operational standards required to keep the supply chain protected.
High-Complexity Fraud Tactics in the New Era of Cargo Theft
Attackers strike where the digital and physical worlds collide. Here’s how they do it:
- “MC Aging Farms”
You can no longer rely exclusively on aging metrics without auditing recent changes to a carrier’s corporate structure or physical addresses. Criminals purchase dormant but aged MC numbers (to bypass “time-in-business” filters in onboarding systems) or build fake credit histories. They wait months to strike during a single weekend, stealing dozens of high-value loads simultaneously before Monday morning rolls around. - Telematics Spoofing
Blindly trusting an automated tracking link is no longer enough. Using advanced software or manipulating the Electronic Logging Device (ELD) API, criminals alter GPS signals. This makes it look like the truck is heading toward its final destination when, in reality, the freight is being diverted elsewhere. - TMS Hijacking and Phantom Routing
According to CrowdStrike data, valid account abuse represented 35% of cloud incidents, reinforcing that identity has become central to intrusions. In this type of scam, attackers use targeted phishing against dispatch employees to access the TMS and silently change the drop-off location on the Rate Confirmation or Bill of Lading (BOL). Your legitimate carrier innocently delivers the freight straight into the hands of thieves. - AI-Enhanced Social Engineering (Vishing)
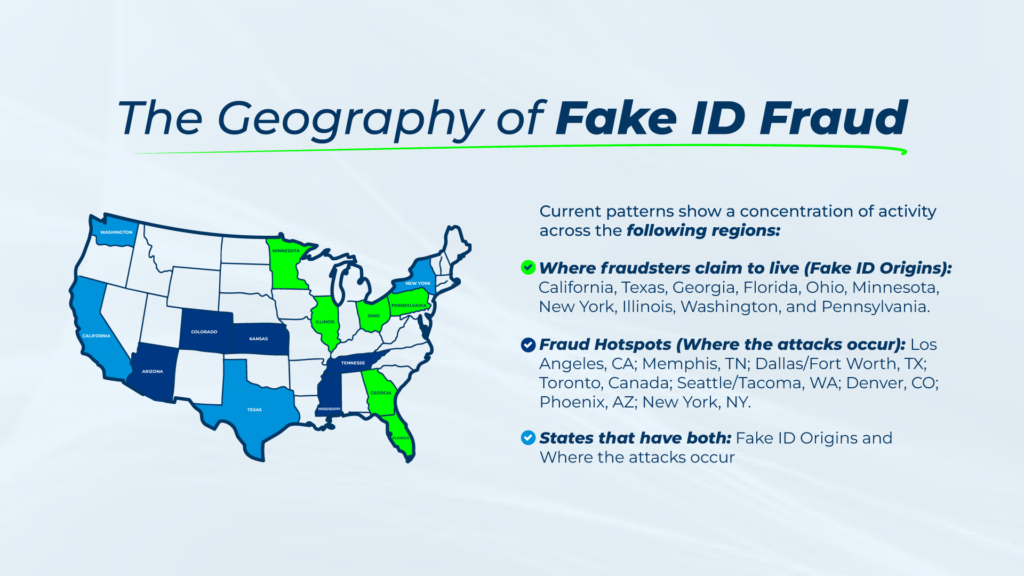
By monitoring the load, scammers contact the driver in transit, posing as the broker or the shipper. Using a strong sense of urgency, they redirect the truck to a fake “inspection” facility. Sometimes, they even use AI to clone the voices of known executives—a technique that a global McAfee study reveals affects 1 in 4 people. - Physical Infiltration with Fake IDs
Adding to these cyberattacks is an audacious physical practice. Criminals dispatch drivers to distribution centers equipped with high-quality forged Commercial Driver’s Licenses (CDLs). By deceiving security personnel at the warehouse gate, they manage to drive away with the freight, posing as the legitimate assigned carrier and successfully completing the theft.
The New Industry Standard: Countermeasures for the New Era of Cargo Theft
At this level of sophistication, standard security measures are no longer enough. Protecting your operations now requires a shift from basic controls to disciplined, intelligence-driven execution:
- Predictive alerts and anti-fraud intelligence to keep operations safe: Looking at an MC’s age isn’t enough. Analyze PDF metadata on Certificates of Insurance (COI) to detect digital tampering, and use network anomaly detection. If an IP connects from a suspicious VPN or a Dark Web node, the system must block the load assignment instantly.
- Modern operations demand a strict security architecture: Mandatory Multi-Factor Authentication (MFA) for any routing changes is paramount. If the delivery address changes after the truck is loaded, it must be verified via a direct voice call with the corporate contact.
- Rapid execution and preferred-carrier capacity for critical loads: When facing an imminent risk or contingency, relying on public load boards is dangerous. You need a closed ecosystem of highly vetted, trusted carriers that allows you to react instantly, ensuring the freight moves quickly and securely.
Navigating this complex threat landscape alone is a high-stakes gamble. This is where partnering with a specialized Third-Party Logistics (3PL) provider like GLT Logistics becomes a critical advantage. By combining rigorous carrier vetting, enterprise-grade validation technology, and tailored cargo insurance, we protect both your operations and your financial exposure.
Navigating this complex threat landscape alone is a high-stakes gamble. This is where partnering with a specialized Third-Party Logistics (3PL) provider like GLT Logistics becomes a critical advantage. By combining rigorous carrier vetting, enterprise-grade validation technology, and tailored cargo insurance, we protect both your operations and your financial exposure.
And if an unexpected anomaly does occur, accountability is our standard: we don’t point fingers or offer excuses—we fix problems and execute rapid solutions. When you move your freight with GLT, you’re not just securing capacity. You’re leveraging the infrastructure and intelligence needed to stay ahead of today’s cyber-physical threats.
Is your supply chain prepared to protect its critical loads from this new generation of cybercriminals? Let’s assess your vulnerabilities and build a more resilient operation against these emerging threats. Contact us here! —we’re here to help you protect your freight.